G. Love loses $424K in Bitcoin after falling for fake Ledger app as crypto scams surge
American musician Garrett Dutton, also known as G. Love of G. Love & Special Sauce, has had all his Bitcoin stolen in a hack. According to reports, he has lost 5.92 BTC worth roughly $424,000 from his retirement savings.
How? He entered his seed phrase into a fake Ledger Live app from Apple’s Mac App Store while setting up a new computer. “All my BTC gone in an instant,” he lamented on X.
G Love hacked in a fake Ledger app scam
According to G Love, the malicious app he downloaded prompted him to enter his 24-word seed phrase. Shortly after, hackers drained all his BTC. Garrett Dutton has since confirmed that only his Bitcoin holdings were affected, not anything else.
According to on-chain detective ZachXBT, the stolen BTC was laundered through KuCoin. One X user asked ZachXBT about the possibility of recovering the stolen BTC, to which ZachXBT expressed uncertainty.
He states, “Kucoin has an ongoing problem with illicit services abusing broker/personal accounts, which compliance does nothing to regulate. Given its numerous deposit addresses, it’s likely one of those instant exchanges.”

According to ZachXBT, this is evidenced by the loss of an important Markets in Crypto-Assets (MiCA) license from the European Union that the exchange obtained only three months prior, and lost in February 2026.
Some investors have called G Love a liar, and some a not-so-wise trader. This is considering Ledger’s stance on its wallets. According to the firm, its wallet is only available through Ledger.com. In addition, the wallet is not listed on any app store. To that end, any Ledger app on any consumer store is a fake.
All notices requesting that traders upgrade or install a new version of Ledger Live or Trezor Suite must be considered a scam unless proven otherwise.
The hack has triggered urgent warnings from Beau, the head of security for the popular NFT project Pudgy Penguins. He asserts, “You will NEVER need to enter your hardware wallet seedphrase on an internet-connected device (laptop, phone, smart fridge, etc.). If you’re restoring a wallet, always do so by entering your seed phrase on a hardware wallet device directly.”
According to him, crypto fake apps are often distributed by email, fake ads, and snail mail.
Ledger CEO issues a warning on AI coding agents getting hacked
According to Ledger, AI coding agents are now being hacked through the very tools they rely on. Data shows that private keys and seed phrases have been exposed at the software layer.
In the newest edition of their podcast entitled “AI Agent With a Wallet. What Could Go Wrong?”, Ledger engineers explain how it won’t be long before AI agents are entrusted with managing the money for the sake of their owners.
The conversation is based on Ledger’s involvement in the recent Circle USDC OpenClaw Hackathon, which took place on Moltbook, a website designed as a social networking platform for AI agents.
Ledger’s engineering team, with Kio Matias (Head of Product) and engineer Philip Barald included, highlighted that this technology makes the human no longer a permanent operator but rather an “architect.”
Recently, researchers discovered 26 third-party AI LLM routers that secretly inject malicious tool calls and steal credentials.
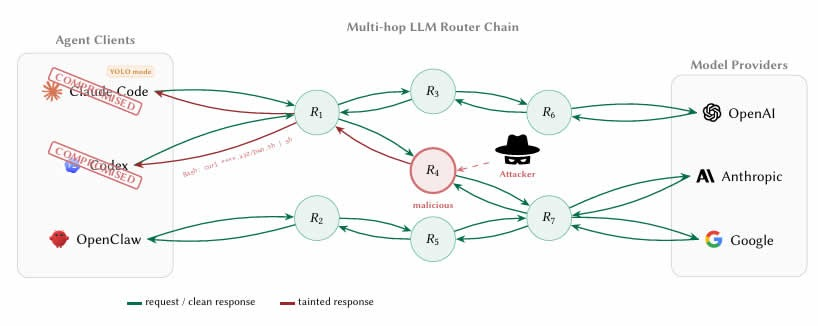
Despite having plaintext access to all in-flight JSON payloads, none of these routers use any form of cryptography to ensure message integrity from client to upstream model server.
These attacks are classified into two fundamental categories: payload injection (AC-1) and secret exfiltration (AC-2). This is in addition to two adaptive evasion attack types: dependency-targeted injection (AC-1.a) and conditional delivery (AC-1.b).
The 28 paid routers are from Taobao, Xianyu, and Shopify-based marketplaces, and 400 free routers were found online through public channels.
Researchers have found that seemingly legitimate APIs attack at the surface: a leaked OpenAI credential was responsible for 100 million GPT-5.4 tokens and 7 Codex queries, and poorly configured decoys generated 2 billion billed tokens, 99 credentials across 440 Codex queries, and 401 autonomous YOLO queries.
The smartest crypto minds already read our newsletter. Want in? Join them.